By incorporating these account tamperproof measures into blockchain design, developers can enhance the security and integrity of user accounts within the decentralized ecosystem. However, it's essential to stay vigilant against evolving threats and adapt security measures accordingly. Continual improvement and adherence to best practices will fortify blockchain systems against malicious attacks, fostering trust and confidence among users and stakeholders.
Digital Signatures
: Implement digital signatures to verify the origin and integrity of messages. When a user signs a message with their private key, anyone with access to the public key can verify the signature, ensuring the message hasn't been tampered with.1. Cryptographic Hash Functions:
Title: Implementing Account TamperProof Measures in Blockchain Design
MultiSignature Wallets
: Employ multisignature wallets that require multiple signatures from different parties to authorize transactions. This approach adds an extra layer of security by necessitating consensus among multiple stakeholders before executing critical operations.
Periodic Auditing
: Conduct regular audits of account data and blockchain transactions to identify discrepancies or unauthorized changes. Auditing ensures compliance with security policies and regulations while proactively addressing any potential vulnerabilities.4. Access Control and Permissions:
RealTime Monitoring
: Deploy monitoring tools to track account activities and detect suspicious behavior in realtime. Anomalies such as unexpected account access or unusual transaction patterns can trigger alerts for further investigation.
Salting
: Incorporate a salt—a random data string—into the hashing process to add complexity and uniqueness to hashed values. Salting prevents attackers from using precomputed hash tables (rainbow tables) to crack hashed values efficiently.
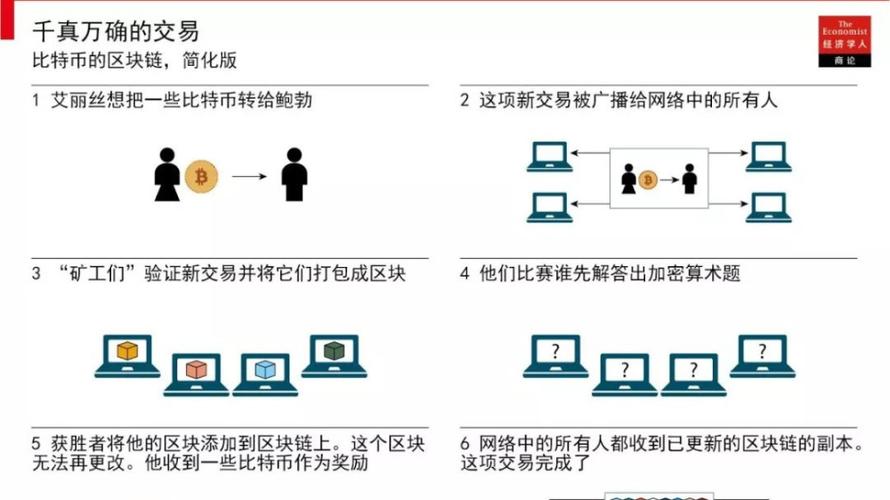
Decentralization
: Distribute copies of the blockchain ledger across a network of nodes to prevent a single point of failure and mitigate the risk of data manipulation. Decentralization ensures that no single entity can alter the records retroactively without consensus from the majority of network participants.
RoleBased Access Control (RBAC)
: Implement RBAC to enforce access control policies based on user roles and permissions. Only authorized users with the appropriate role can perform specific actions on the blockchain network, reducing the surface area for potential attacks.2. Public Key Infrastructure (PKI):
[End of Document]
Public/Private Key Pair
: Leverage PKI for secure authentication and transaction signing. Each user possesses a unique public/private key pair. Transactions are signed with the private key and verified with the corresponding public key, ensuring the authenticity and integrity of transactions.Conclusion:
In the realm of blockchain technology, ensuring the integrity and security of user accounts is paramount. Account tampering undermines trust in the system and can have severe consequences for users and businesses alike. Implementing robust measures to prevent and detect tampering is essential for maintaining the reliability and credibility of a blockchain network. Let's delve into some key strategies for designing account tamperproof measures in blockchain systems:
5. Continuous Monitoring and Auditing:
3. Immutable Ledger:
Hashing Account Data
: Utilize cryptographic hash functions like SHA256 to hash sensitive account data such as passwords, private keys, and account details. Hashing obscures the original data while providing a unique identifier, making it computationally infeasible for attackers to reverseengineer the original data.
Blockchain Consensus Mechanisms
: Employ consensus mechanisms such as Proof of Work (PoW) or Proof of Stake (PoS) to achieve agreement on the order and validity of transactions. Once a transaction is recorded on the blockchain, it becomes immutable and resistant to tampering, providing a secure audit trail of account activities.标签: 防篡改特性? 区块链设计账户防篡改措施包括 区块链如何保证数据不被篡改 区块链防篡改可追溯 区块链设计账户防篡改措施有哪些